Advanced Persistent Threats
Advanced Persistent Threats are sneaky, hard-to-detect malware that resides on your network, often aimed at stealing financial account information. APTs are all about the behavior of a very patient and slow-moving attacker. They are a kind of malware that waits for an opportunity to strike and leak out your data secretly.
The APT lifecycle begins with an entry point on a computer network – perhaps an infected USB device or a phishing email. Once the APT has begun to spread throughout the network, it also begins to report back to a command and control (C&C) server, providing it with data and hiding itself from detection.
The primary goal of most APT attacks is to achieve and maintain ongoing access to a targeted network rather than to get in and out as quickly as possible. A great deal of effort and resources can go into carrying out APT attacks and hackers typically select high-value targets, such as nation-states and large corporations, with the goal of stealing information over a long period of time. The attacker’s motives are varied, as they may target intellectual property to gain a competitive advantage in certain industries.
Other targets may include power distribution and telecommunications utilities or other infrastructure systems, social media, media outlets, and electoral and other political targets. Organized crime groups may sponsor advanced persistent threats to gain information they can use to carry out criminal acts for financial gain.
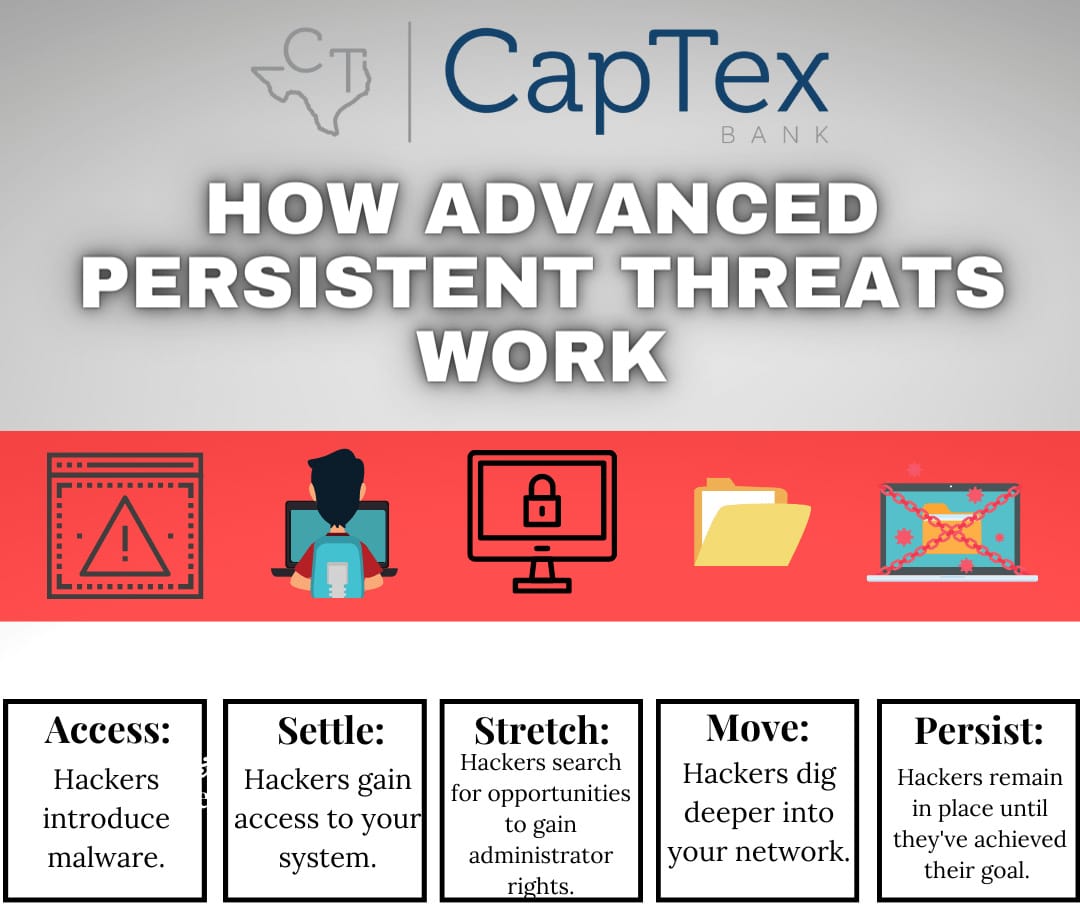
Advanced persistent threats are carried out in multiple phases, reflecting the same basic sequence of gaining access, maintaining and expanding access, and attempting to remain undetected in the victim’s network until the goals of the attack have been accomplished. Advanced persistent threats focus on establishing multiple points of compromise. They usually attempt to establish multiple points of entry to the targeted networks, which enables them to retain access even if the malicious activity is discovered and incident response is triggered. The warning signs may be hard to detect and symptoms include:
- Unusual activity on user accounts
- Extensive use of backdoor Trojan horse malware
- Odd or uncharacteristic database activity
- Presence of unusual data files
A key strategy for preventing the introduction of APTs onto your systems is for users to be aware and not share account details, recognize phishing attempts and to browse safely on the web. Layers of defense within your technology infrastructure enhance protection against the introduction of APTs. Other prevention measures include, limiting access to devices, implementing strong user access controls, and monitoring device logs.